Thomas Grønning Knudsen, recently joined ELEMENTS as Head of Integrations & Security. Making the move from M2 Film in Denmark, Thomas brings with him over 20 years worth of industry experience and insight.
Having developed a love of technology from a very young age, Thomas’ curiosity, reverse engineering attitude and his desire to make the world a smarter one, have all been driving forces in his successful career to date. Having been an integral part of the industry since the early 90s, working in a number of important roles, Thomas made the move to M2 Film in 2005, first as an editor and then as a motion graphics designer, which led to him working on more compositing and VFX projects before moving into the role of Head of IT & Security in 2012.
First encountering the ELEMENTS team at IBC in 2012, Thomas immediately felt an affinity to the people and the product, highlighting how exciting it was that ELEMENTS was centred around the users’ needs rather than what a systems engineer might invent for someone. So when the opportunity came to work for the company Thomas happily accepted, after 16 successful years at M2 Film.

You’ve joined the company in the capacity of Lead Integration and Security Specialist. Do you feel like this is an area of the industry that is more relevant than ever, given just how rapidly technology is advancing?
You could argue that integration and security are sort of opposites. Something really secure is somewhat locked by nature, so the challenge of making things communicate and collaborate while still being extremely secure requires a lot of considerations. For example, creating an “integration” between two prisons, so that people can easily move about while protecting the overall structure is complicated, so the “merge” of these two roles and “disciplines” makes total sense in my head. You wouldn’t want to join two components together without understanding the impact this could have on other structures and the overall architecture and workflows of the system.
I have seen examples where developers spend quite a lot of time hardening a web-based portal, while still allowing an iOS app to connect with no requirement for a complex PIN code or Touch-ID at all and “remember me” set by default to easily allow the user in. So now the entire ecosystem security relies on the user’s passcode on their phone alone, and that could be as simple as 1-2-3-4. So it’s really important to consider every little component in the setup and how it could impact the overall system integrity and security.
Do you agree that one of the biggest challenges for most media companies is how they allow their users to collaborate whilst still ensuring maximum confidentiality and integrity?
The challenge with the creative business, as seen from a security standpoint, is that the users are creative and they have a business need for exchanging ideas and work with so many people on a daily basis. Typically we are not talking about small files, so the system needs to allow for sharing large portions of files fast as well. If you work in a bank, you expect everything to be 100% locked down, and no one will question that all doors are closed. But creative directors have a hard time understanding why they can’t do all their work in their private Dropbox or share files using other public sharing services. And if you don’t make everything easily available to the users, they will start inventing new ways on their own. So with creative minds on the team, you have to ensure that you have a strong and secure collaboration setup that is easy to use. Ease of use is what prevents users from taking a walk down the shadowy IT pathway, which is something that is dangerous and hard to control in many organisations.
I have seen many examples where a security team spend all of their time protecting the setup of a system, with several firewalls, rapidly changing passwords and numerous technical limitations, without considering how the user thinks and what would make sense to them. And in the end, they send stuff on their own phone, printing out documents or connecting using an online service that can help them out. And that colour print they made might just end up getting lost somewhere (remember, paper is also information technology).
With my old company M2 Film, we implemented Darktrace, the world’s leading autonomous cyber defence platform that inspects all network traffic in real time using AI, flagging when something unusual happens. This allowed us to be more relaxed on a daily basis, knowing that if someone does something careless, it will get noticed. But apart from this, there were not too many restrictions in place – just the regular security measures and strong collaboration setups like ELEMENTS.
A great number of companies restrict their systems, which has a knock-on effect in terms of how users can collaborate and benefit from a lot of built-in features and sharing functions. Do you think there are skilful ways around this and do you think companies can configure their systems in such a way, that collaboration can still be undertaken and used to its full potential?
We have seen lots of examples where companies buy a system like ELEMENTS or other collaboration tools, and then end up not leveraging any of the cool features at all, which is a shame, especially when viewed from a developer’s point of view.
With creative minds on the team, you have to ensure that you have a strong and secure collaboration setup that is easy to use.
Thomas Grønning Knudsen, Head of Integrations & Security, ELEMENTS
Being compliant and working under ISMS frameworks, like the ISO/IEC 27001, will naturally put lots of restraints on how users are able to work, and working “around” ISO is not something you just do. But sometimes, you need to think of your system as not being ELEMENTS alone, but being ELEMENTS in the context of a larger implementation. So instead of saying “Box A is not allowed to talk to Box B” because of our policy, it might help if you place A and B in the same “container” and consider them as a whole. How can this new “system” be allowed to communicate with the world? Taking a step back and viewing your setup from an aerial perspective before just saying “yes” or “no” as to whether components can be allowed to communicate, is time well spent.
When implementing an ISMS, you need to identify any information security controls not applicable to your company or business. ISO 27001 addresses this by specifying the need to conduct a risk assessment to determine which information security controls are required. ISO 27002 specifies information security control objectives, providing best practice means of achieving those objectives. And since you need to introduce your own security policies, it’s important to update existing policies with the objectives of your new desired workflow. Then comes the process of performing a risk assessment to manage and mitigate the identified risks. For each of the controls identified as applicable to your organisation, ISO 27002 will have the necessary implementation guidance. None of the above is easily achieved, and you will need to update some policies and procedures to get your final system in compliance again.
You have previously referred to yourself as a technical Swiss Army knife due to your wide ranging skill set and passion for knowledge. What industry developments and new ways of working are really exciting to you at this point in time?
As a child I would disassemble all kinds of technical devices to see how they worked (my grandmother’s old watch for instance), and most of the time I was able to put the pieces back together. This curiosity has stayed with me, and my “reverse engineering” attitude, combined with an urge to make my world “smarter”, drives my love for automation and scripts, to help me avoid doing the same task too many times.
One area of technology that is really taking off and never fails to amaze and astonish me is AI (artificial intelligence) through deep learning and CNN (convolutional neural network), especially when combined with “computer vision”, which is showing some very exciting promise right now.
It would be nice to finish on an ELEMENTS related topic and find out what you’re most looking forward to being a member of the team here.
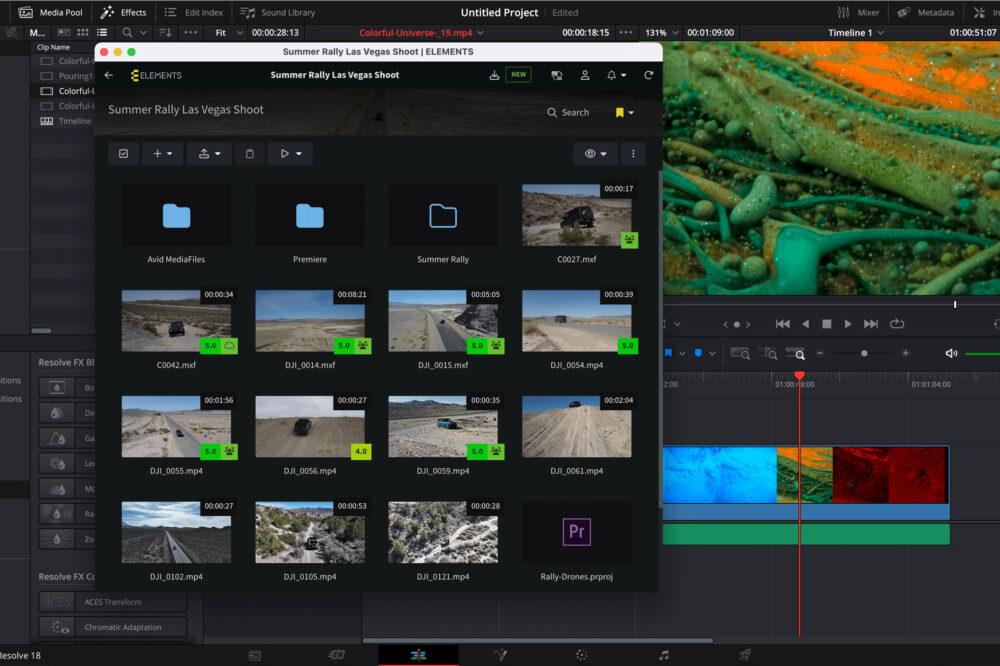
ELEMENTS is already a super strong and secure product, featuring awesome integrations with other technology partners. I’m really looking forward to being a part of this amazing team, to further connect and secure the ecosystem, allowing future creatives to put themselves at the centre of the creative process, rather than having technical challenges stand in their way.
This curiosity has stayed with me, and my “reverse engineering” attitude, combined with an urge to make my world “smarter”, drives my love for automation and scripts, to help me avoid doing the same task too many times.
Thomas Grønning Knudsen, Head of Integrations & Security, ELEMENTS
The world is rapidly changing to allow for new ways of working, whether that is from home or anywhere in the world, where users have access to the tools they love and need. This is something that would have seemed impossible years ago.
Video and media traditionally involve super heavy files, with new large formats like 4K / 8K, so turning that into seamless cloud-based workflows sounds almost impossible, but ELEMENTS is up to the challenge, and we have some super exiting new ideas and products in the pipeline.